Cybersecurity Solutions










Protect & Manage Digital Assets
Security frameworks designed to safeguard data, ensure regulatory compliance, enforce access policies, manage risk, and maintain resilient technology environments.
Cybersecurity Deployment and Configuration Capabilities
Antivirus Deployment
Enterprise endpoint protection rollout with centralized management, policy enforcement, threat detection, and automated update governance.
Data Protection
Implementation of data encryption, secure storage, backup alignment, and policy-based access controls to safeguard sensitive information.
Access Control Systems
Deployment of role-based authentication, multi-factor verification, and directory integration for controlled resource access across systems.
CCTV Integration
Networked camera setup with secure storage, access permissions, monitoring protocols, and integration with physical security policies.
Cybersecurity Implementation
End-to-end deployment of structured security policies, monitoring systems, incident response workflows, and governance practices across IT environments.
Cybersecurity Architecture and Deployment Scope

Firewall Installation & Configuration
Deployment and rule configuration for perimeter and internal firewalls including traffic filtering, VPN setup, logging, and threat mitigation alignment.
Expertise we provide :
- Traffic filtering
- VPN setup
- Rule configuration
- Logging
- Threat mitigation
- Policy alignment
Antivirus Deployment
Endpoint protection rollout with centralized management, update automation, threat quarantine, reporting, and compliance enforcement.
Expertise we provide :
- Endpoint install
- Policy enforcement
- Updates automation
- Threat quarantine
- Reporting
- Compliance check
Data Protection
Implementation of encryption, secure storage, access restrictions, backup integration, replication, and data integrity validation.
Expertise we provide :
- Encryption
- Secure storage
- Access control
- Backup integration
- Replication
- Integrity check

Access Control Systems
Deployment of identity management, role-based permissions, multi-factor authentication, audit logging, directory integration, and policy governance.
Expertise we provide :
- Role setup
- MFA config
- Permissions mapping
- Audit logging
- Directory integration
- Policy enforcement
CCTV Integration
Networked camera deployment with secure access, storage policies, monitoring dashboards, and integration with operational security protocols.
Expertise we provide :
- Camera setup
- Network integration
- Storage config
- Access permissions
- Monitoring setup
- Security policies
Cybersecurity Implementation
End-to-end execution of security frameworks including monitoring, incident response, vulnerability scanning, policy documentation, and governance enforcement.
Expertise we provide :
- Monitoring
- Incident response
- Vulnerability scanning
- Policy documentation
- Governance
- Compliance review

Seamless IT Integration

Enhanced Cybersecurity Protection

Cloud Migration Success

24/7 IT Support
AI-Powered Automation

Network Infrastructure Upgrade
Case study
Featured Case Studies
Coretech Solutions takes pride in our clients’ success. Learn how our collaboration can drive your business results in selected stories of partnership.
Businesses commonly face threats such as phishing attacks, ransomware, malware infections, insider threats, and unauthorized access attempts that can compromise sensitive data and disrupt operations.
Cybersecurity protects critical business systems, confidential data, and digital assets from cyber threats, helping organizations avoid financial losses, operational disruption, and reputational damage.
Organizations usually require services such as firewall protection, endpoint security, threat monitoring, vulnerability assessments, access control management, and security compliance support.
Businesses can reduce cyber risks by implementing multi-layered security strategies including firewalls, encryption, access controls, continuous monitoring, and regular employee cybersecurity awareness training
If a breach occurs, the organization should immediately initiate incident response procedures, isolate affected systems, remove threats, analyze the attack source, and implement recovery and security improvements.
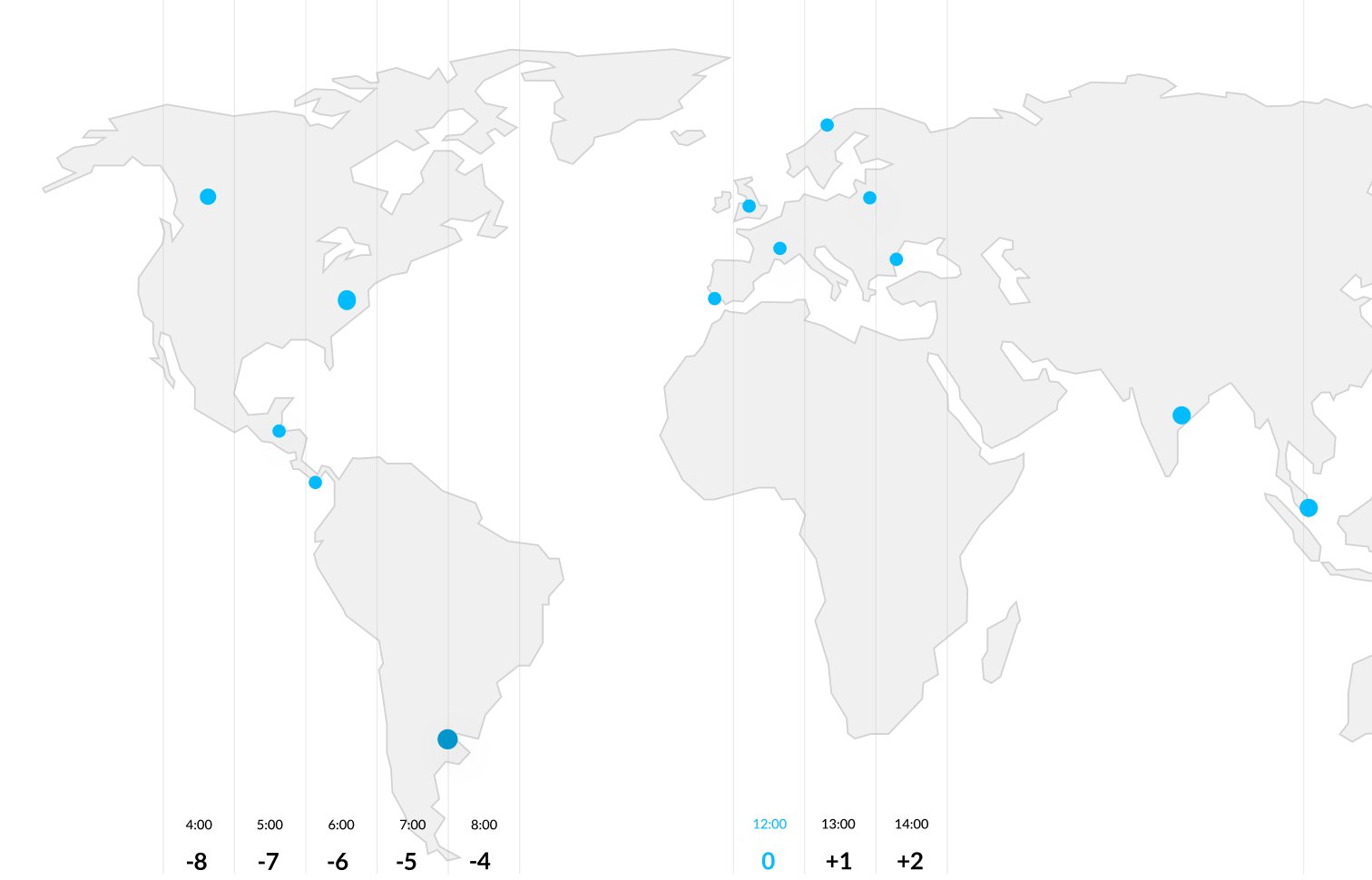
You can find us here
We have a strong global presence, marking our commitment to delivering tech excellence in key markets worldwide.

United States
Chicago
789 Windy City Drive, Floor 3 Chicago, IL 60601, USA

United kingdom
Chicago
789 Windy City Drive, Floor 3 Chicago, IL 60601, USA